Microsoft 365 has quickly become the mainstay software of many companies worldwide. A process which began a number of years ago with software and services moving to the cloud quickly accelerated when Covid arrived and remote working became the norm. Working from home became a regular and necessary occurrence, and with that came new requirements
Application management can be a burden even for the most well-resourced IT teams. There is a pressure to offer a plethora of applications to keep users productive. The result is that IT face a relentless flow of admin-heavy work simply to keep the portfolio of applications running. This involves running deploying and managing hundreds and
Defending distributed networks against advanced persistent threats. When it comes to hybrid work, there are many network security implications to consider. As IT teams build more distributed, flexible networks, the challenge of identifying persistent threats and detecting unwanted network activity in encrypted traffic increases. The necessity for remote work has accelerated investment in more flexible,
Microsoft 365 is set to receive the first substantive cost update since its launch. Are you prepared? Microsoft 365 Price increases – What is happening and when? Microsoft has announced that beginning March 2022 there will be a price increase on most, if not all, of the Microsoft 365 products that they supply. At the
Industry trends affect how small and medium-sized retailers do business The pandemic caused an unprecedented shift in commerce. Customers want more retail experiences that are contactless, flexible, and online. Small and medium-sized retail businesses that adapt can better serve their customers. For example, businesses that rely on in-store sales might offer virtual, appointment-based shopping sessions or
Our ITAnywhere solution has been utilised by many of our customers for several years. This platorm is about to get a major make over in the form of IT Anywhere v3. But what does this really mean? This is a platform where all your key IT systems sit, fully managed in our secure cloud, encompassing your
Challenges law firms face today The pandemic caused an unprecedented shift across industries, and many law firms are struggling to adapt. These days, law firms need to give their clients alternative ways to discuss their cases without meeting in person. Similarly, lawyers and staff need to be able to access sensitive case data whether at
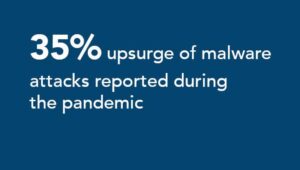
Cybercrime is rising at an unprecedented rate. Here is a guide on cybercrime types and tips to protect against them. Key Points Cybercrime is mounting against individuals, businesses and governments. Common types of cybercrime include identity theft, ransomware and denial of service attacks. Organizations can help thwart attacks through services such as email protection, business
Learn about the top ransomware attacks in 2021, and what they teach us about how to protect your business and employees from future attacks. 2021 Ransomware Attacks that Shook the World Key Points Ransomware attacks surged in 2021, affecting organizations across industries and impacting our everyday lives. The costs of ransomware not only
Create future-ready experiences for everyone No matter how you look at it, creating memorable experiences for employees and customers is table stakes for success, growth, and staying competitive. As your business plans for the future, robust hybrid workplace technologies will be critical in reconnecting with the people most important to you. To ease your transition to a
Ransomware Attacks Are Increasing Due To Low-Cost Tools And Vulnerable Targets, With High Chances Of Profits And Minimal Risk. Key Points: Ransomware attacks are on the rise thanks to wide availability of low-cost tools to non-programmers; ransomware is relatively low risk with high reward potential. Organizations are only as secure as their partners and suppliers.
Over the course of a weekend in 2020, organizations around the world pivoted from in-person workplaces to either fully remote or hybrid remote/in-person work models. For security teams, this raised a concerning question: How do you protect the perimeter when said perimeter no longer exists? This is where cloud-native security – a term we at